The malware GoldPickaxe, targeting iPhone users in Vietnam and Thailand, retrieves login information, including facial data, thereby bypassing biometric security layers.
GoldPickaxe is considered one of the first malware to successfully exploit the iOS platform. This malware shares the same origin as GoldDigger, developed by the GoldFactory group, which was uncovered by the security firm Group-IB in mid-last year.
In a cybersecurity alert issued by the Cybersecurity Authority of the Ministry of Information and Communications in February, there was a case where a user in Hanoi was tricked into installing fake public service software. The software required video verification, and by the next day, this person’s stock account had been sold off and billions of VND were transferred away.
According to Group-IB, this may indicate that GoldPickaxe is now targeting Vietnamese users. “Based on the specific request to scan faces, along with the fact that GoldFactory is operating in the region, we suspect they may have begun exploiting GoldPickaxe in Vietnam,” Group-IB assessed.

An iPhone performing a facial scan. (Photo: Lưu Quý).
During the Asian Banking and Finance Conference held in Ho Chi Minh City in mid-March, the emergence of GoldPickaxe raised concerns among many organizations. According to Mr. Troy Lê, a representative from BShield, a security tool supporting numerous large applications in Vietnam, this malware is dangerous because it has been successfully exploited on both iOS and Android platforms, while also collecting users’ biometric data. As Thailand has implemented biometric authentication, including facial recognition, for large transactions, and Vietnam is soon to adopt this method, GoldPickaxe poses a new challenge for users and platforms in protecting accounts.
How does GoldPickaxe infiltrate accounts?
Initially, attackers will attempt to introduce the malware-laden application onto the victim’s device through social engineering tactics. In the case of the victim in Hanoi mentioned earlier, they impersonated a government agency to lure the user into installing the fake public service software. In Thailand, a common scenario recorded is the use of software for tax refunds and bill payments.
For Android, users only need to install the application via a APK file. On the other hand, for iOS, the perpetrators will exploit Apple’s app testing platform, TestFlight, or convince victims to install a Mobile Device Management (MDM) profile to gain complete control over the device.
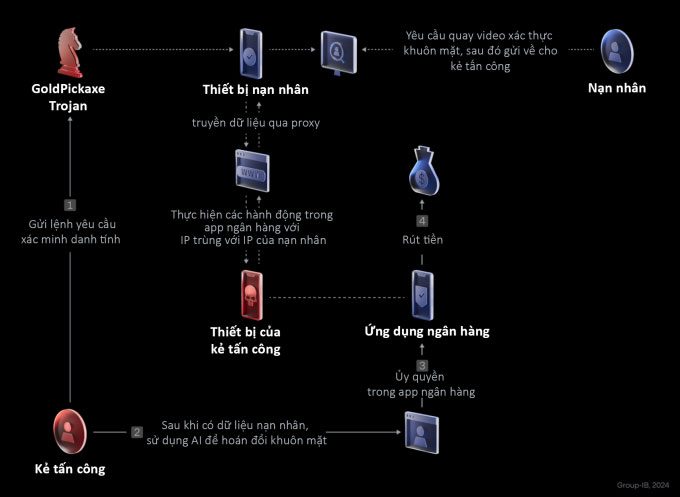
The attack mechanism of GoldPickaxe. (Photo: Group-IB).
Once infiltrated, GoldPickaxe activates permissions such as filtering SMS and accessing the Internet. At the same time, the counterfeit application will require users to verify their identity with personal documents and record a video. This video is sent back to the hacker’s server, becoming material for creating deepfake technology, which can swap faces using AI.
According to expert Troy Lê, the malware silently collects personal information from the user’s device and secretly logs the activities and inputs, creating log records. Additionally, it gathers facial data, which may include the victim’s IP address to replicate, tricking services into believing it is the actual user.
“With this data, the attacker does not need to directly carry out unauthorized transactions from the victim’s phone. Instead, they gather all necessary information to access the banking application from another device,” Mr. Troy Lê stated.
How to stay safe from GoldPickaxe?
The Cybersecurity Authority has continuously issued warnings, advising users against providing personal information or installing unknown applications to avoid account theft. However, in reality, the scenarios and methods of attack frequently change, causing many people to fall victim despite being vigilant.
From the perspective of the security platform developer, Mr. Troy Lê believes that banks and financial organizations must proactively implement measures to mitigate risks for users.
After deploying BShield for many financial applications in Vietnam, Mr. Troy Lê noted that many platforms and services still have vulnerabilities, such as lacking detection mechanisms for unsafe devices to take timely preventive measures; the application processes lack continuous monitoring mechanisms. This allows hackers to bypass initial checks of applications to control the victim’s account. Additionally, some applications may be exploited through API vulnerabilities, allowing malware to interfere with and alter the application’s operation, enabling hackers to carry out attacks in between.
“Financial and banking applications are always a top target for hackers. Therefore, they must build protective mechanisms for their users and their services,” this expert advised.
According to Group-IB, the malware from the GoldFactory group has many features that can easily deceive users, such as issuing fake alerts from banking applications, fake call screens, and messages enticing victims to perform certain actions. Users should remain vigilant if they notice unusual signs such as excessive battery drain, overheating, strange notifications, high data usage, or applications requesting excessive permissions.