Increasingly, denial-of-service attacks are being used by cybercriminals to take down their enemies and disrupt businesses that operate online.
 |
Source: Pctipp |
Exploiting DNS servers—often viewed as the phonebook of the internet—hackers have amplified the power of DDoS attacks to maximum levels, leaving their targets with no chance of resistance.
Earlier this year, VeriSign experienced “growing pains” when their network systems faced an unprecedented wave of large-scale attacks. Only last week did VeriSign discover that these “barrage” attacks did not originate from the usual botnet computers. Instead, they were taking “fire” from DNS system servers.
New Weapons, New Forms
“DNS has now become the new weapon of DDoS“, stated security expert Dan Kaminsky. With this new weapon, denial-of-service attacks have undergone significant changes, from targets to difficulty levels. “Now, even those without slave computers to command can carry out attacks“.
Whether conducted via botnets or DNS servers, the target systems (which can include web servers, name servers, or mail servers) all face the same fate—they are overwhelmed by a massive flood of data sent simultaneously from multiple locations across the internet. As a result, the victim’s website becomes inaccessible in any form, or it freezes when attempting to process the incoming data flood.
Quick Questions – Brief Answers |
| Why can DNS be exploited to execute DDoS attacks? Up to 75% of all DNS servers are overly open to requests from the internet. This response feature needs to be disabled by administrators as soon as possible. How is the DDoS attack using DNS carried out? What is the level of amplification of DNS? Why does using DNS help protect hackers? Why can’t this form of attack be stopped? |
Denial-of-service attacks were once the “toys” of bored teenagers, treating website takedowns as a pastime. However, today, DDoS attacks are often initiated by cybercriminals to extort money from e-commerce businesses, especially lucrative ones like gambling sites or adult entertainment platforms. If companies refuse to pay a ransom, their website will be inundated with DDoS traffic.
In other instances, competitors of the targeted website have hired hackers to conduct DDoS attacks, naturally in a secretive and discreet manner.
Unlike slave computers, DNS servers are “good and valuable citizens” of the internet. This system plays an essential role in connecting web users, mapping character domain names like www.cnet.com to numeric IP addresses that computers typically use.
In this new form of attack, hackers often use a botnet to simultaneously send multiple requests to DNS servers, causing them to open up. These requests are cleverly crafted to trick the DNS servers into thinking they come from the victim (who is being flooded with data). Typically, the DNS server will respond (or resolve the character address into a numeric IP string) back to that network address, directing all query results to the targeted victim.
Using DNS servers offers numerous benefits to attackers. They not only disguise their actual systems, making it very difficult for victims to trace the source of the attack, but more importantly, DNS servers can amplify the strength of the attack many times over compared to a botnet.
Dirty Tactics
Using DNS servers to amplify the intensity of attacks can be likened to stuffing someone’s mailbox by writing and sending numerous emails. However, emails are relatively easy to trace back, and writing them takes a considerable amount of time.
A more effective method is to send a series of postcards requesting responses (similar to magazine subscriptions), pre-filled with the sender’s address being the target that will be attacked. The DNS server will be misled and respond to that request.
Typically, DDoS attacks using botnets can still be thwarted by blocking the outgoing data flow from zombie computers (identifying zombies is feasible). However, blocking requests from DNS servers is far more complex. This is because DNS servers play an extremely significant role in the normal operation of the internet. If you block the traffic (in and out) of a DNS server, you inadvertently prevent legitimate users from sending emails or visiting other websites.
“That is why this form of attack is so dirty“, stated Rob Fleischman, CTO of Simplicita. “In the future, the DNS system will definitely be abused more, and we need stronger security controls for DNS“.
No Room for Laziness
Currently, there are about 7.5 million DNS servers in operation, and the number of “welcoming” servers, ready to accept any requests from the outside, is unpredictable, potentially ranging from 600,000 to as many as 5.6 million servers.
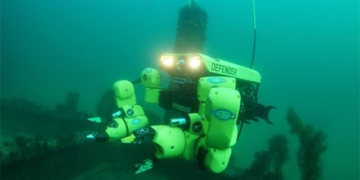
Security experts advise that organizations using DNS servers should immediately disable the aforementioned “recursive” feature or adjust security settings so that only authorized personnel can access this feature. Targets of DDoS attacks can protect themselves by implementing special defense technologies from companies like Prolexic Technologies.
DNS is increasingly being exploited in DDoS attacks, and it is time for administrators to stop being negligent.
Tien Yi