In recent years, the information technology sector has witnessed a boom in the wireless networking industry. Wireless communication capabilities have become almost essential in handheld devices (PDAs), laptops, mobile phones, and other digital devices.
In recent years, the information technology sector has witnessed a boom in the wireless networking industry. Wireless communication capabilities have become almost essential in handheld devices (PDAs), laptops, mobile phones, and other digital devices.
With superior features such as flexible connectivity coverage, rapid deployment, and decreasing costs, wireless networks have become one of the competitive solutions that can replace traditional Ethernet LAN networks. However, the convenience of wireless networking also poses significant security challenges for network administrators. The advantages of wireless connectivity can diminish due to the difficulties arising in network security.
When designing technical requirements for wireless networks, the IEEE 802.11 standard has taken data transmission security into account through the WEP encryption method. This method is supported by most wireless device manufacturers as a default security measure. However, recent discoveries regarding vulnerabilities in the 802.11 WEP standard have heightened concerns about the safety of WEP and spurred the development of the 802.11i standard. Nevertheless, the majority of current wireless devices still use WEP, and it will likely persist for quite some time before the 802.11i standard is widely accepted and implemented.
This article aims to provide a brief overview of the WEP protocol, its operational mechanism, its vulnerabilities, and preventive measures, while also presenting an optimal WEP configuration method for small and medium-sized networks.
WEP Protocol
WEP (Wired Equivalent Privacy) refers to security equivalent to wired networks (Wired LAN). This concept is part of the IEEE 802.11 standard. By definition, WEP was designed to ensure that wireless networks maintain a level of security comparable to traditional wired networks. For LANs (as defined by the IEEE 802.3 standard), data security during transmission against external attacks is ensured through physical restrictions, meaning that hackers cannot directly access the wired transmission system. Thus, the 802.3 standard does not impose encryption measures to prevent unauthorized access. In contrast, the 802.11 standard prioritizes data encryption due to the nature of wireless networks, which cannot physically limit access to the transmission medium; anyone within the coverage area can access data if it is unprotected.
| TERMINOLOGY Stream Cipher: A method of encrypting data bit by bit. In contrast to block cipher, which encrypts data in blocks (typically 64 bits). |
WEP (Wired Equivalent Privacy) provides security for data on wireless networks through encryption using the symmetric algorithm RC4, developed by Ron Rivest of the renowned RSA Security Inc. The RC4 algorithm allows for variable key lengths, which can be up to 256 bits. The 802.11 standard mandates that WEP-enabled devices support a minimum key length of 40 bits, while also ensuring options for longer keys. Currently, most wireless devices supporting WEP offer three key lengths: 40 bits, 64 bits, and 128 bits.
Using the RC4 encryption method, WEP ensures the confidentiality and integrity of information on wireless networks, while also functioning as an access control method. A wireless device without the correct WEP key cannot access the Access Point (AP) and cannot decrypt or modify data in transmission. However, recent findings from security analysts reveal that by capturing a large number of encrypted data packets using WEP and employing suitable tools, it is possible to accurately deduce the WEP key in a short time. This vulnerability arises from flaws in how WEP employs the RC4 encryption method.
Limitations of WEP
Since WEP uses RC4, a stream cipher, a mechanism is needed to ensure that two identical pieces of data will not yield the same result when encrypted twice differently. This is crucial in data encryption to limit the ability of hackers to guess the key. To achieve this, a value known as the Initialization Vector (IV) is used in conjunction with the key to create different keys for each encryption. The IV is a 24-bit value, and the IEEE 802.11 standard recommends (but does not mandate) that it be changed with each data packet. Because the sending device generates the IV without following any specific rules or standards, it must be sent to the receiving device in an unencrypted form. The receiving device will use the IV value along with the key to decrypt the data packet.
The use of the IV value is the source of most problems with WEP. Since the IV value is transmitted unencrypted and placed in the header of 802.11 data packets, anyone who “captures” the data on the network can see it. With a length of 24 bits, the IV can have approximately 16,777,216 variations. Security experts at the University of California, Berkeley discovered that when the same IV is used with the same key on an encrypted data packet (a concept informally referred to as an IV collision), a hacker can capture the data packet and determine the WEP key. Additionally, cryptanalysis experts Fluhrer, Mantin, and Shamir (FMS) have identified weaknesses in the IV generation algorithm for RC4. FMS outlined a method for detecting and exploiting faulty IVs to discover the WEP key.
Moreover, one of the greatest dangers is that the methods of attack using the two aforementioned techniques are passive. This means that an attacker only needs to capture data packets in transit without needing to communicate with the Access Point. This makes it extremely difficult—if not nearly impossible—to detect WEP key-finding attacks.
Currently, there are tools available on the Internet capable of finding WEP keys, such as AirCrack (Figure 1), AirSnort, dWepCrack, WepAttack, WepCrack, and WepLab. However, using these tools requires extensive knowledge and they have limitations regarding the number of data packets that need to be captured.
Optimal WEP Solutions 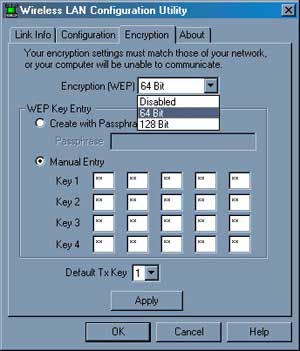 Given the serious vulnerabilities of WEP and the widespread availability of WEP key-finding tools on the Internet, this protocol is no longer a recommended security solution for networks with high information sensitivity. However, in many current wireless devices, WEP remains the commonly supported data security solution. Nonetheless, the vulnerabilities of WEP can be mitigated if properly configured and supplemented with additional security measures.
Given the serious vulnerabilities of WEP and the widespread availability of WEP key-finding tools on the Internet, this protocol is no longer a recommended security solution for networks with high information sensitivity. However, in many current wireless devices, WEP remains the commonly supported data security solution. Nonetheless, the vulnerabilities of WEP can be mitigated if properly configured and supplemented with additional security measures.
To enhance the security level of WEP and complicate attempts by hackers, the following measures are recommended:
• Use a WEP key of 128 bits: Typically, WEP-enabled devices allow for key configuration in three lengths: 40 bits, 64 bits, and 128 bits. Using a 128-bit key increases the number of packets a hacker must capture to analyze the IV, making it more difficult and prolonging the time needed to decrypt the WEP key. If your wireless device only supports WEP at 40 bits (commonly found in older wireless devices), you should contact the manufacturer to download the latest firmware update.
• Implement a policy for periodic WEP key changes: Since WEP does not support automatic key rotation, changing the key regularly can be inconvenient for users. However, if the WEP key is not changed frequently, it should be done at least once a month or whenever there is suspicion that the key may have been compromised.
• Utilize tools to monitor data statistics on the wireless transmission: Since WEP key-finding tools require capturing a large number of packets and hackers may need to use data generation tools, spikes in data traffic can be indicative of a WEP attack, alerting network administrators to detect and implement timely countermeasures.
The Future of WEP
As mentioned in previous sections, WEP (802.11) does not provide the necessary security for most wireless applications requiring high safety standards. Due to the use of fixed keys, WEP can be easily cracked with available tools. This has led network administrators to seek non-standard WEP solutions from manufacturers. However, since these solutions are not standardized, they complicate the integration of devices from different manufacturers.
Currently, the 802.11i standard is being developed by the IEEE to address the vulnerabilities of WEP and to serve as a complete replacement for WEP once approved and widely implemented. However, the official approval date for the 802.11i standard has not yet been announced. Therefore, the Wi-Fi Alliance of wireless manufacturers has proposed and widely disseminated the WPA (Wi-Fi Protected Access) standard as an interim measure before the official implementation of 802.11i. Technically, WPA is the latest iteration of 802.11i and ensures compatibility between devices from different manufacturers. As of now, several new Wi-Fi devices have supported WPA and WPA2, resolving WEP’s security issues.
Conclusion
Despite its serious drawbacks, WEP security is still better than having no encryption mechanism at all for wireless networks! WEP can be seen as a low-level security mechanism, necessary to deploy when better options cannot be used. This is suitable for scenarios involving older wireless devices that do not support WPA, or situations with low security requirements such as home wireless networks or community wireless networks.